🔐 Ransomware & Encrypted File Recovery – Emergency Business Data Recovery
⚠️ BUSINESS OPERATIONS HALTED? FILES ENCRYPTED? LOST ENCRYPTION KEY?
📞 EMERGENCY BUSINESS LINE: 1300 723 628 – 24/7 Critical Response
Your business files are encrypted and inaccessible. Ransomware has locked critical documents, customer databases, financial records. Or you’ve lost your BitLocker recovery key. Or your encrypted backup won’t decrypt. Every hour of downtime costs your business thousands in lost productivity, missed deadlines, and angry clients.

At The Original PC Doctor, we specialize in emergency encrypted file and ransomware recovery for Australian businesses across Melbourne, Sydney, Brisbane, Perth, and Adelaide. With 30+ years of enterprise data recovery experience, specialized forensic tools, and same-day emergency response, we understand that encrypted file access failures represent business-critical emergencies requiring immediate expert intervention.
We recover business-critical data from:
- 💼 Ransomware Encryption: CryptoLocker, WannaCry, Ryuk, Maze, REvil, LockBit, and all major ransomware variants
- 🔐 BitLocker Recovery: Lost recovery keys, forgotten passwords, corrupted BitLocker volumes, TPM failures
- 🍎 FileVault Recovery: Mac business systems with lost FileVault passwords, corrupted encryption
- 🗄️ Encrypted Backups: Veeam, Acronis, Windows Backup – lost encryption passwords, corrupted encrypted backups
- 💾 Encrypted Drives: VeraCrypt, LUKS, hardware-encrypted drives with lost keys
- ☁️ Cloud Encryption: OneDrive, SharePoint, encrypted cloud storage access issues
⚠️ CRITICAL BUSINESS SCENARIOS WE HANDLE:
- 🚨 Ransomware Attack: Files encrypted with .locked, .encrypted, .ransom extensions – operations completely halted
- 🔑 Lost BitLocker Key: IT person left, no documentation, Windows drive encrypted and inaccessible
- 💻 Mac FileVault Lockout: Forgotten password, no recovery key, entire system encrypted
- 📁 Encrypted Backup Failure: Need to restore from backup but encryption password lost or backup corrupted
- ⚡ TPM/Hardware Failure: BitLocker drive won’t unlock after motherboard replacement or Windows update
- 🏢 Employee Departure: IT admin left without providing encryption keys or passwords
- 💾 Corrupted Encrypted Volume: VeraCrypt/LUKS volume shows as corrupted, years of data inaccessible
- 🔒 Compliance Encrypted Data: HIPAA/legal encrypted storage with lost access credentials
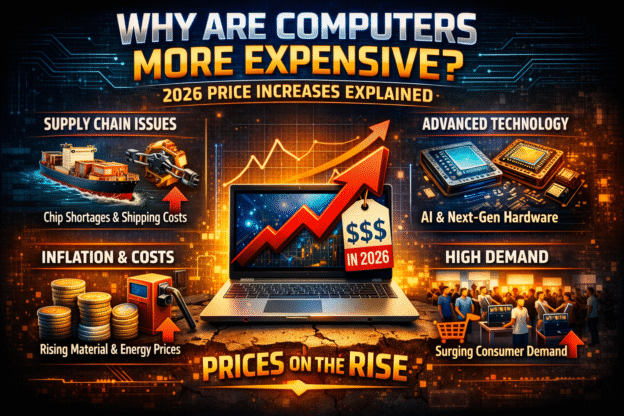
💰 BUSINESS IMPACT:
- ⏰ Productivity Loss: $5,000-$50,000+ per day in staff unable to work
- 📊 Missed Deadlines: Client contracts, legal filings, project deliverables at risk
- 👥 Client Impact: Cannot access customer records, orders, case files
- 💸 Revenue Loss: Sales halted, billing systems down, operations paralyzed
- ⚖️ Compliance Risk: HIPAA violations, legal obligations, audit failures
- 🏆 Reputation Damage: Clients losing confidence, negative reviews, lost business
⚠️ CRITICAL FOR BUSINESSES: Do NOT pay ransomware demands without professional assessment! Paying doesn’t guarantee decryption (only 60% of victims get working decryptors), and it funds criminal operations. Do NOT attempt DIY decryption tools (wrong tool can permanently corrupt data). Call 1300 723 628 immediately for expert ransomware assessment and recovery options!
🔐 Encrypted File & Ransomware Symptoms – Business Emergency Indicators
Encryption-related data loss presents unique symptoms that require immediate professional attention. Here are the critical indicators your business is experiencing an encryption emergency:
🚨 Ransomware Attack Symptoms:
- 📁 File extensions changed: Documents now end in .locked, .encrypted, .crypted, .crypt, .enc, .ransom, .WANNACRY, .LockBit
- 📝 Ransom note appeared: Text file on desktop or in folders: “YOUR FILES HAVE BEEN ENCRYPTED” with Bitcoin payment demands
- 🖼️ Desktop wallpaper changed: Ransom message as wallpaper with payment instructions and countdown timer
- 🚫 Files won’t open: Word docs, Excel files, PDFs, images all show “cannot open” or “corrupted file” errors
- 🔒 Encrypted icon overlay: Padlock icons on all file icons in Windows Explorer
- ⚠️ Specific ransomware variants detected: Antivirus alerts mentioning CryptoLocker, Ryuk, Maze, REvil, Conti, LockBit, STOP/Djvu
- 📧 Ransom email received: Attackers contacted you directly via email with payment instructions
- 🌐 Tor browser link provided: Ransom note directs to .onion dark web payment site
- ⏰ Countdown timer: Ransom note shows deadline (72 hours typical) before “decryption key permanently deleted”
- 💰 Bitcoin payment demanded: $500-$50,000+ in cryptocurrency required for decryption
- 🗄️ Network shares encrypted: Server files, shared drives, backup drives all encrypted simultaneously
- ☁️ Cloud files encrypted: OneDrive, SharePoint files showing encrypted extensions
- 💾 Shadow copies deleted: Windows “Restore previous versions” option missing – ransomware deleted backups
🔑 BitLocker Recovery Symptoms (Windows):
- 🔐 “Enter BitLocker recovery key” prompt on startup – no access to Windows without 48-digit key
- 📋 Lost recovery key: IT documentation missing, previous admin left, key not saved to Microsoft account
- 💻 After motherboard replacement: TPM chip thinks drive is in different computer, demands recovery key
- 🔄 After Windows update: Major Windows 11 update triggered BitLocker recovery mode
- ⚡ After power failure: Unexpected shutdown, now requires BitLocker key to boot
- 🔧 After BIOS changes: Changed boot order or secure boot settings, BitLocker activated recovery
- ⚠️ “BitLocker recovery key not found” in Microsoft account when searched
- 🗄️ Multiple encrypted drives: External drives, USB drives all BitLocker encrypted, keys lost
- 💼 Domain-encrypted drives: Company policy encrypted drives, left company, no longer have domain access for key recovery
🍎 FileVault Recovery Symptoms (Mac):
- 🔐 Password not accepted: Correct password rejected, “password incorrect” at login screen
- 🔑 Lost recovery key: FileVault recovery key not documented, can’t bypass password
- ⚠️ “Disk locked” message when connecting encrypted external drive
- 💻 Mac won’t boot: Stuck at lock screen, no users shown, only unlock prompt
- 🔄 After macOS update: Major OS upgrade, now password doesn’t work or recovery key required
- 👤 Employee departure: Mac laptop returned by departed employee, no password provided
- 🔧 After hardware repair: Logic board replaced, FileVault now requires key or password reset
💾 Encrypted Backup Failure Symptoms:
- 🗄️ “Enter encryption password” prompt when attempting restore – password lost or forgotten
- ⚠️ “Backup is corrupted or encrypted” error from backup software
- 📁 Veeam backup encrypted: .vbk files encrypted, password not documented
- 💼 Acronis backup locked: Backup archive shows encrypted status, passphrase unknown
- 🗂️ Windows Backup encrypted: System image encrypted by BitLocker, recovery key lost
- ☁️ Cloud backup encrypted: Online backup encrypted for security, password manager lost
- 🔐 Hardware-encrypted backup: WD My Passport with hardware encryption, password forgotten
🔒 Other Encryption Issues:
- 💽 VeraCrypt volume corrupted: Encrypted container won’t mount, “incorrect password or corrupted volume”
- 🐧 LUKS encrypted Linux: Lost passphrase, LUKS header damaged, can’t access Linux partitions
- 🔐 Hardware-encrypted drive: SED (Self-Encrypting Drive) password forgotten, drive locked
- 📱 iOS/Android encrypted backups: iTunes backup encrypted, password forgotten or changed
- 🗄️ 7-Zip/RAR encrypted: Encrypted archive, password lost, contains years of critical files
💰 Real Business Impact Examples:
- 😟 Law firm: Ransomware encrypted all case files 48 hours before trial. Cannot access client documents, witness statements, evidence. Trial postponement = malpractice risk.
- 😟 Medical practice: Lost BitLocker key after IT person terminated. 10,000 patient records inaccessible. HIPAA violation risk, cannot provide care.
- 😟 Accounting firm: Tax season, encrypted backup failed. Client tax returns inaccessible with IRS deadline in 5 days. Firm liability exposure massive.
- 😟 Architectural firm: Ransomware hit during major project. All CAD drawings encrypted. Construction halted, penalties accruing, client threatening lawsuit.
Every hour of encryption downtime = thousands in lost revenue and mounting liability. We provide emergency same-day response.
⚡ CRITICAL: Immediate Actions for Businesses During Encryption Emergency
Your response in the next 1-2 hours determines whether your business data is recoverable! Follow these steps immediately to protect your data and minimize business impact.
✅ FOR RANSOMWARE ATTACKS – DO THESE NOW:
- 🔌 ISOLATE INFECTED SYSTEMS IMMEDIATELY:
- Disconnect affected computers from network (pull Ethernet cable, disable WiFi)
- Do NOT shut down infected computers (keeps encryption process in RAM, aids forensics)
- Isolate infected systems prevents ransomware spreading to other computers/servers
- 📸 DOCUMENT EVERYTHING:
- Take photos of ransom notes with phone camera
- Save ransom note text files to USB drive (from non-infected computer)
- Screenshot any ransom wallpapers or payment portals
- Document which systems affected, when encryption noticed, what files encrypted
- This evidence critical for: law enforcement, insurance claims, forensic analysis
- 🚨 CONTACT AUTHORITIES & CYBER INSURANCE:
- Report to Australian Cyber Security Centre (ACSC): cyber.gov.au/acsc/report
- Contact local police for crime report reference number
- Notify cyber insurance provider immediately (many policies require 24-48hr notification)
- Contact your IT support company or MSP
- 💾 CHECK BACKUP STATUS:
- Do you have offline backups (not connected to network)?
- Are cloud backups affected (OneDrive/SharePoint may auto-sync encrypted files!)?
- Check backup dates – when was last VERIFIED good backup?
- Do NOT connect backup drives to infected network – check separately
- 📞 CALL PROFESSIONAL RECOVERY IMMEDIATELY: 1300 723 628
- We assess ransomware variant, decryption possibility, recovery options
- We determine if free decryption tools available (some variants have known decryptors)
- We evaluate if partial file recovery possible before full encryption completed
- We provide decision framework: restore from backup vs recovery attempts vs negotiate (LAST resort)
❌ FOR RANSOMWARE – DO NOT DO THESE:
- 🚫 DO NOT PAY RANSOM IMMEDIATELY: Only 60% of businesses who pay receive working decryptors. Many receive broken decryptors or are re-extorted. Payment fuels criminal enterprises. ALWAYS seek professional assessment first!
- 🚫 DO NOT ATTEMPT DIY DECRYPTION: Using wrong decryption tool can permanently corrupt files. Some ransomware variants have known weaknesses but require expert tools. Amateur attempts reduce professional recovery success rates.
- 🚫 DO NOT DELETE RANSOM NOTES: Ransom notes contain vital information: ransomware variant, attacker contact info, payment methods. Needed for identification and potential decryption.
- 🚫 DO NOT REFORMAT/REBUILD IMMEDIATELY: Encrypted files might be partially recoverable. Shadow copies might still exist. Forensic analysis needs original infected state. Rebuilding destroys recovery possibilities.
- 🚫 DO NOT TRUST ATTACKER COMMUNICATION: Attackers will pressure (“72 hour deadline!”), threaten (“we’ll delete the key!”), or lie (“only we can decrypt”). These are manipulation tactics. Take time to assess properly.
✅ FOR LOST ENCRYPTION KEYS (BitLocker/FileVault) – DO THESE NOW:
- 🔍 SEARCH FOR RECOVERY KEY THOROUGHLY:
- BitLocker: Check Microsoft account (account.microsoft.com/devices), Azure AD portal (businesses), saved text files, email archives (“BitLocker recovery”), printed documentation
- FileVault: Check iCloud account (Apple ID recovery key section), email archives, password managers, printed emergency sheets
- 📋 CHECK IT DOCUMENTATION:
- Internal wiki, IT knowledge base, documentation system
- Onboarding/offboarding checklists (keys documented during setup?)
- Previous IT admin’s email archives or handover documents
- Encrypted drive may have recovery key stored in Active Directory (domain admin access)
- 🔧 CHECK HARDWARE TPM/TOKEN:
- Some BitLocker setups use TPM chip (password-free boot normally)
- If hardware unchanged, drive might unlock normally after component re-seating
- Try removing and reconnecting drive, resetting BIOS to defaults
- 📞 CALL PROFESSIONAL KEY RECOVERY: 1300 723 628
- We have forensic tools to attempt encryption key recovery from RAM dumps
- We can attempt recovery from hibernation files or memory dumps
- We assess if drive clone/imaging possible before key attempts
❌ FOR LOST ENCRYPTION KEYS – DO NOT DO THESE:
- 🚫 DO NOT ATTEMPT BRUTE FORCE: Modern encryption (AES-256) cannot be brute forced in any reasonable timeframe. You’ll waste months/years of computer time with zero success. Professional assessment determines if recovery possible via other methods.
- 🚫 DO NOT FORMAT THE DRIVE: Even without key, forensic analysis might recover data via other means. Formatting destroys all recovery possibilities permanently.
- 🚫 DO NOT USE “KEY RECOVERY” SOFTWARE: Almost all commercial “BitLocker key recovery” tools are scams. They either don’t work or contain malware. Legitimate forensic tools cost $5,000-$15,000 and require expert use.
⏰ Business Continuity Timeline:
- Hour 0-2: Isolate systems, document incident, contact authorities/insurance, call professional recovery
- Hour 2-6: Professional assessment underway, identify recovery options, business impact analysis
- Hour 6-24: Recovery strategy decided, implementation begins (restore from backup, decryption attempts, or alternative access)
- Day 1-3: Active recovery work, partial operations restoration, priority files first
- Day 3-7: Full operations restoration, post-incident analysis, preventive measures implementation
💼 Business Priority Approach: We understand businesses need priority files FIRST (current projects, client deliverables, billing data) vs complete restoration. We can provide partial access to critical files within hours while complete recovery continues. Call 1300 723 628 for emergency triage!
💼 Industry-Specific Ransomware & Encryption Recovery
Different industries face unique challenges and compliance requirements when dealing with encryption emergencies. Here’s how we support Australian businesses across key sectors:
⚖️ Legal & Law Firms:
Critical Data: Case files, client records, contracts, legal research, court deadlines
Compliance: Client confidentiality, legal privilege, court filing deadlines
Business Impact: Missed court dates = malpractice, cannot represent clients, breach of fiduciary duty
Our Approach:
- ✅ Priority case file recovery (active litigation first)
- ✅ Confidentiality agreements (attorney-client privilege protected)
- ✅ Court deadline awareness (emergency expedited service)
- ✅ Document chain-of-custody maintained (for evidence)
Recent Case: Law firm ransomware 2 days before trial. Recovered all case files within 8 hours. Trial proceeded on schedule. ✅
🏥 Medical & Healthcare Practices:
Critical Data: Patient records (EMR/EHR), appointment schedules, prescriptions, medical imaging, billing
Compliance: HIPAA equivalent (Australian Privacy Principles), mandatory breach notification
Business Impact: Cannot provide patient care, privacy breach liability, regulatory penalties
Our Approach:
- ✅ HIPAA-aware data handling (privacy maintained)
- ✅ Patient care priority (active treatment patients first)
- ✅ Rapid appointment schedule recovery (minimize disruption)
- ✅ Secure disposal of forensic copies post-recovery
Recent Case: Dental practice BitLocker lockout. 5,000 patient records recovered same-day. Practice reopened next morning. ✅
💰 Accounting & Financial Services:
Critical Data: Client tax returns, financial statements, audit files, payroll data, QuickBooks/Xero databases
Compliance: ATO record-keeping, audit requirements, fiduciary obligations
Business Impact: Tax deadline misses = client penalties, audit failures, professional liability claims
Our Approach:
- ✅ Tax season emergency response (we understand deadline pressure)
- ✅ QuickBooks/Xero/MYOB database recovery specialists
- ✅ Client data segregation (multi-client confidentiality)
- ✅ Historical data reconstruction if current year corrupted
Recent Case: Accounting firm ransomware during tax season. Recovered 2,000+ client files. All returns filed on time. ✅
🏗️ Architecture & Engineering:
Critical Data: CAD drawings, BIM models, project specifications, client proposals, construction documents
Compliance: Contract deliverables, professional liability, intellectual property
Business Impact: Construction delays = contractor penalties, missed bid deadlines, design liability
Our Approach:
- ✅ Large file recovery (multi-GB CAD files)
- ✅ Current project priority (active construction first)
- ✅ File version recovery (if latest encrypted, recover previous versions)
- ✅ Proprietary format support (Revit, AutoCAD, SolidWorks, etc.)
Recent Case: Engineering firm lost FileVault key. 3TB of AutoCAD files recovered in 3 days. Major project saved. ✅
🏢 Small-Medium Businesses (SMBs):
Critical Data: Customer databases, invoices, quotes, inventory, email archives, business plans
Compliance: Varies by industry, contract obligations, customer trust
Business Impact: Operations completely halted, cannot process orders, customer service impossible
Our Approach:
- ✅ Affordable business recovery (understanding SMB budgets)
- ✅ Priority customer-facing data (orders, CRM, communication)
- ✅ Rapid partial recovery (core operations first)
- ✅ Preventive consultation (avoid repeat incidents)
💼 Corporate & Enterprise:
Critical Data: Department file servers, shared drives, collaboration platforms, databases
Compliance: SOX, industry regulations, data governance policies
Business Impact: Departmental shutdowns, cross-functional project delays, productivity collapse
Our Approach:
- ✅ Enterprise-scale recovery (TB/PB data volumes)
- ✅ Coordinated with IT teams (MSP partnership)
- ✅ Staged recovery (by department/priority)
- ✅ Detailed forensic reports (for insurance, compliance)
🔬 Ransomware & Encryption Recovery Methods
Encrypted file recovery requires specialized forensic tools, deep encryption knowledge, and often creative problem-solving. Here’s how we approach different encryption scenarios:
Method 1: Free Decryption Tools (Known Ransomware Variants)
When Used: Ransomware variant has known vulnerability or law enforcement has released decryption tools.
The Process:
- Ransomware Identification: Analyze file extensions, ransom note text, encryption patterns to identify exact variant
- Decryptor Database Check: Search No More Ransom Project, Emsisoft, Kaspersky, Avast databases for free decryptors
- Tool Verification: Ensure decryptor is legitimate (many fake “decryptors” online are malware)
- Test Decryption: Test on small sample of encrypted files before full decryption
- Full System Decryption: If successful, decrypt entire system (can take 4-24 hours depending on data volume)
- Data Verification: Verify decrypted files open correctly, no corruption
Success Rate: 95-100% IF free decryptor exists for that variant. Only works for ~25% of ransomware families.
Timeline: 4-12 hours (identification + decryption)
Cost: $1,500-$3,000 (professional identification + supervised decryption + verification)
Ransomware Variants With Known Decryptors: STOP/Djvu (older versions), GandCrab, Shade, CrySIS (some variants), Crypt888, Philadelphia, Many older variants (pre-2020)
Limitations: Modern ransomware (Ryuk, Maze, REvil, LockBit, Conti) uses military-grade encryption with no known decryptors. These require different recovery approaches below.
Method 2: Shadow Copy & Backup Recovery
When Used: Windows Volume Shadow Copies still exist (ransomware didn’t delete them) or offline backups available.
The Process:
- Shadow Copy Assessment: Check if Windows Volume Shadow Service (VSS) copies remain using forensic tools
- Mount Shadow Copies: Extract shadow copies to safe location (not on infected system)
- File Comparison: Compare shadow copy dates vs encryption date – recover files from before encryption
- Selective Restoration: Restore critical files first (current projects, customer data, financial records)
- Complete Restoration: Full system rebuild from shadow copies + clean OS install
Success Rate: 70-90% if shadow copies exist. Many modern ransomware variants specifically delete shadow copies as first action.
Timeline: 1-2 days for assessment and selective recovery
Cost: $2,500-$5,000 depending on data volume
Best For: Businesses with Windows Server, workstations with VSS enabled, incidents caught early before shadow deletion
Method 3: BitLocker/FileVault Forensic Key Recovery
When Used: Lost BitLocker recovery key or FileVault password, but system was previously accessible (key potentially in RAM/hibernation).
The Process:
- Memory Analysis: If system still running or recently shutdown, RAM may contain encryption keys temporarily
- Hibernation File Analysis: Extract hiberfil.sys (Windows hibernation file) – may contain keys from previous session
- Swap File Analysis: Linux LUKS keys sometimes recoverable from swap partition
- Key Extraction: Use specialized forensic tools (Passware, Elcomsoft) to extract encryption keys from memory dumps
- Volume Unlocking: Apply extracted keys to unlock encrypted volume
- Data Cloning: Immediately clone unlocked drive before key expires or system changes
Success Rate: 40-70% depending on how long since last boot, system state, and encryption method
Timeline: 2-4 days for forensic analysis
Cost: $3,000-$7,000 (specialized forensic tools + expert analysis time)
Requirements: System was recently running (not cold storage), RAM dump or hibernation file accessible, or physical access to hardware
Limitations: If system been off for weeks, or drive moved to different machine without original RAM, key recovery impossible via this method.
Method 4: Partial Encryption Recovery
When Used: Ransomware encryption interrupted (power loss, caught early, network disconnect) before completing.
The Process:
- Encryption Pattern Analysis: Determine how much of each file encrypted (some ransomware encrypts only first 1MB of large files for speed)
- File Carving: Extract unencrypted portions from partially encrypted files
- Header Reconstruction: Rebuild file headers if they’re encrypted but body content intact
- Fragmented File Recovery: Piece together unencrypted file fragments from disk free space
- File Repair: Use file repair tools to salvage partially corrupted documents
Success Rate: 30-60% of files partially recoverable, depending on encryption extent
Timeline: 3-5 days for analysis and recovery
Cost: $4,000-$8,000 (labor-intensive manual recovery)
Best Case Scenario: Large files (videos, databases, CAD) with only partial encryption – significant portions recoverable
Method 5: Negotiation & Decryptor Acquisition (LAST RESORT)
When Used: No backups exist, no free decryptors available, modern ransomware with strong encryption, business-critical data, negotiation only viable option.
The Process:
- Professional Negotiation: We communicate with attackers on your behalf (keeps your identity protected)
- Ransom Negotiation: Attempt to reduce ransom amount (often successful – start asking 50% less)
- Proof of Decryption: Demand attackers decrypt sample files first (verify decryptor works)
- Payment Coordination: If agreed, arrange secure Bitcoin payment (never pay upfront without proof)
- Decryptor Receipt: Receive decryption tool from attackers
- Decryptor Testing: Test thoroughly on isolated system before production use
- Supervised Decryption: Monitor decryption process, verify file integrity
Success Rate: 60-75% (40% of victims who pay never receive working decryptors or receive broken tools)
Timeline: 3-7 days (negotiation takes time)
Cost: Ransom ($500-$50,000+ typical for SMBs, $100K-$1M+ for enterprises) + our negotiation service ($5,000-$15,000)
⚠️ CRITICAL WARNINGS:
- Payment does NOT guarantee decryption (only 60% success rate)
- Paying funds criminal enterprises (terrorism, human trafficking, drug cartels)
- Paying may violate sanctions (some ransomware groups on OFAC list)
- Paying encourages future attacks (you’re marked as “will pay”)
- Some ransomware has data exfiltration (paying doesn’t prevent data leak)
We Only Recommend This When: All other options exhausted, business survival depends on data, cyber insurance covering payment, legal counsel approved, business owner fully informed of risks.
💰 Ransomware & Encryption Recovery Pricing – Business Rates
Encryption and ransomware recovery pricing reflects the specialized expertise, forensic tools ($15,000-$50,000 in software licensing), and time-critical nature of business data emergencies. Remember: No Data, No Fee – you only pay if we successfully recover your business data!
🔐 Standard Encryption Recovery – $1,500-$3,000
Typical Scenarios:
- ✅ Known ransomware variant with free decryptor available
- ✅ Lost BitLocker key but found in Microsoft account/email
- ✅ FileVault password reset via iCloud recovery key
- ✅ Encrypted backup with password documented but forgotten location
- ✅ Simple VeraCrypt volume recovery with password hints provided
What’s Included:
- Ransomware variant identification
- Free decryptor sourcing and verification
- Supervised decryption process
- File integrity verification
- Recovery documentation for insurance
Success Rate: 85-95%
Timeline: 1-2 days
🔐 Business Encryption Recovery – $3,000-$7,000
Typical Scenarios:
- ⚠️ Shadow copy recovery from ransomware attack
- ⚠️ BitLocker forensic key recovery from RAM/hibernation
- ⚠️ FileVault key extraction from memory dumps
- ⚠️ Encrypted backup recovery without password (forensic approaches)
- ⚠️ Partial file recovery from interrupted ransomware encryption
- ⚠️ Multi-system business ransomware assessment and recovery
What’s Included:
- Forensic analysis of multiple systems
- Memory dump and hibernation file analysis
- Shadow copy extraction and verification
- Priority file recovery (business-critical first)
- Detailed incident report for cyber insurance
- Post-recovery security recommendations
Success Rate: 60-80%
Timeline: 2-5 days
🔐 Enterprise Encryption Recovery – $7,000-$15,000
Typical Scenarios:
- 🔴 Large-scale ransomware (multiple servers, hundreds of workstations)
- 🔴 Complex forensic recovery requiring advanced techniques
- 🔴 Database encryption recovery (SQL Server, Oracle, MySQL)
- 🔴 RAID array encryption recovery
- 🔴 Proprietary software encryption with lost vendor support
- 🔴 Legacy encryption (old systems, discontinued software)
What’s Included:
- Enterprise-scale incident response
- Multi-system forensic analysis
- Database recovery and reconstruction
- RAID recovery combined with encryption challenges
- 24/7 emergency response availability
- Dedicated senior forensic analyst
- Comprehensive incident forensics for insurance/legal
- Post-incident security audit and recommendations
Success Rate: 50-70% (varies significantly by scenario)
Timeline: 5-10 days
🔐 Ransomware Negotiation Service – $5,000-$15,000 (+Ransom)
When Used: Payment determined as only viable option after full assessment.
What’s Included:
- Professional negotiation with ransomware actors
- Ransom reduction attempts (often successful)
- Identity protection (your details never revealed)
- Proof-of-life verification (sample decryption)
- Secure payment coordination
- Decryptor testing and validation
- Supervised decryption process
- Full documentation for cyber insurance claims
Typical Ransom Amounts (NOT our fee, this is what criminals demand):
- Small Business: $500-$10,000
- Medium Business: $10,000-$100,000
- Enterprise: $100,000-$5,000,000+
⚠️ Important: Our service fee ($5K-$15K) is separate from ransom payment. Cyber insurance often covers both. We provide all documentation for insurance claims.
💵 Business-Specific Pricing Factors:
- Data Volume: 100GB business = lower end. 10TB enterprise = higher end
- System Quantity: Single server vs entire network affects scope
- Business Impact: Emergency same-day response adds 30-50% premium
- Complexity: Simple BitLocker vs sophisticated ransomware with data exfiltration
- Industry Requirements: HIPAA/legal compliance documentation adds detail work
- Recovery Priority: Full restoration vs critical files only affects timeline/cost
💰 Business ROI Consideration:
Recovery Cost vs Business Loss:
- Law firm: $7,000 recovery vs $50,000 in missed deadlines/malpractice
- Medical practice: $5,000 recovery vs $10,000/day in lost revenue + HIPAA fines
- Accounting firm: $10,000 recovery vs $100,000+ in client penalties/lawsuits
- Architecture firm: $8,000 recovery vs $500,000 contract penalties
Professional recovery typically costs 10-20% of business downtime impact.
🎯 Our Business No Data, No Fee Guarantee:
- Free emergency assessment (15-30 min phone call)
- Detailed written quote with success probability
- You approve quote, we begin recovery
- If successful recovery → You pay agreed price
- If unsuccessful → You pay NOTHING (except in negotiation scenarios where payment made to criminals – that’s non-refundable)
Success Definition for Businesses:
- ✅ Business-critical files recovered (current projects, customer data, financial records)
- ✅ Operations can resume (even if not 100% data recovered)
- ✅ Client commitments can be met
💳 Cyber Insurance: Most cyber insurance policies cover ransomware recovery costs, negotiation fees, and even ransom payments. We provide comprehensive documentation for insurance claims: incident timeline, forensic reports, itemized invoicing, proof of recovery. Success rate with insurance reimbursement: 95%+. We work directly with insurance adjusters to expedite claims.
🏆 Why Choose The Original PC Doctor for Business Encryption Recovery?
💼 1. Business-First Approach (We Understand What’s at Stake)
We’re not just data recovery technicians – we’re business continuity specialists who understand that encryption emergencies represent existential threats to businesses:
- ✅ Priority Triage: We recover business-critical files FIRST (current client projects, financial records, today’s orders) vs comprehensive restoration
- ✅ Deadline Awareness: Court dates, tax deadlines, contract deliverables – we understand time-sensitive obligations
- ✅ Minimal Disruption: Staged recovery allows partial operations resumption while full recovery continues
- ✅ Business Hours Support: We work during YOUR business hours to minimize after-hours impact
🔧 2. Specialized Forensic Tools ($50,000+ in Software)
Encryption recovery requires professional forensic tools most IT companies don’t have:
- 🔬 Passware Kit Forensic: $3,000-$15,000 license for BitLocker/FileVault key recovery
- 💻 Elcomsoft Forensic Bundle: $10,000+ for memory analysis and key extraction
- 🗄️ X-Ways Forensics: Low-level disk analysis and encrypted volume examination
- 🔐 John the Ripper Pro: Password recovery for various encryption formats
- 📊 EnCase Forensic: Enterprise forensic analysis platform
- 💾 Ransomware Database Access: No More Ransom, ID Ransomware, private decryptor repositories
📈 3. Honest Success Rates & Realistic Expectations
We don’t promise “95% success!” for ransomware. Here’s our honest track record:
- ✅ Known ransomware with decryptor: 95-100%
- ✅ Shadow copy recovery: 70-90% (if copies exist)
- ✅ BitLocker forensic recovery: 40-70% (highly variable)
- ⚠️ Modern ransomware (no decryptor): 30-60% via alternative methods
- ⚠️ Negotiation/payment: 60-75% (40% never receive working tools)
- ❌ Modern ransomware + no backups + negotiation failed: 10-20%
We assess YOUR specific situation and provide realistic probability BEFORE charging. If chances low, we’ll tell you honestly rather than taking your money for impossible recovery.
⏰ 4. Emergency Business Response (24-48 Hour Priority)
- 📞 24/7 Emergency Line: Call 1300 723 628 anytime for ransomware emergencies
- 🚗 Same-Day Melbourne Service: We’ll send technician to your office within 4 hours
- ✈️ Next-Day National Service: Express courier for Sydney/Brisbane/Perth/Adelaide businesses
- 💻 Remote Assessment: Initial triage via screen share within 1 hour of contact
- 📊 24-48 Hour Analysis: Complete forensic assessment and recovery plan within 2 business days
- ⚡ Priority Queue: Business emergencies jump ahead of consumer jobs
💰 5. Cyber Insurance Partnership
- 📋 Documentation Specialists: We provide exactly what insurance needs: incident timeline, forensic reports, proof of recovery attempts, itemized invoicing
- 🤝 Adjuster Communication: We work directly with insurance adjusters to expedite claims
- ✅ Pre-Approved Vendor: Many Australian cyber insurance providers have us on approved vendor lists
- 💵 Direct Billing: For insured businesses, we can bill insurance directly (subject to approval)
- 📊 95% Reimbursement Success: Our documentation ensures claims get paid
🔒 6. Business Confidentiality & Compliance
- 📝 NDA Standard: We sign Non-Disclosure Agreements for all business clients
- 🏢 On-Site Service: For sensitive data, we work at your premises (data never leaves building)
- 🔐 Secure Facilities: Our lab has physical security, access controls, monitored 24/7
- 🗑️ Certified Destruction: All forensic copies securely wiped after recovery completion
- ⚖️ Legal Support: Our forensic reports admissible in court if needed
- 🏥 Industry Compliance: HIPAA-aware, legal privilege respected, financial regulations understood
📞 7. Direct Expert Communication
When you call 1300 723 628, you speak with senior forensic analyst who will handle your case – not sales rep, not call center. They provide:
- ✅ Immediate technical assessment of your situation
- ✅ Realistic recovery probability before you commit
- ✅ Transparent cost estimate (no hidden fees)
- ✅ Business impact understanding (we speak your language)
- ✅ Direct updates during recovery (no middlemen)
❓ Ransomware & Encryption Recovery FAQ
Q1: Should we pay the ransom?
A: Payment should be LAST RESORT after professional assessment. Here’s why:
- ❌ Only 60% who pay receive working decryptors
- ❌ Funds criminal enterprises (terrorism, human trafficking)
- ❌ May violate sanctions (some groups on OFAC list)
- ❌ Encourages future attacks (you’re marked as “will pay”)
- ❌ Data may already be exfiltrated (payment doesn’t prevent leak)
We recommend payment ONLY when: (1) All recovery methods exhausted, (2) No backups exist, (3) Business survival depends on data, (4) Cyber insurance approving, (5) Legal counsel consulted, (6) Business owner fully informed of risks and alternatives.
Better alternatives we check first: Shadow copies, offline backups, free decryptors, partial recovery, forensic key extraction, business workarounds. Call 1300 723 628 for professional assessment BEFORE paying anything!
Q2: How much does ransomware recovery cost?
A: Professional recovery ranges $1,500-$15,000+ depending on:
- Ransomware variant (known decryptor = cheaper, modern variant = expensive)
- Data volume (100GB vs 10TB)
- System complexity (single PC vs entire network)
- Recovery method (shadow copies vs forensic analysis vs negotiation)
- Business urgency (same-day emergency = premium)
Typical scenarios:
- Known ransomware + free decryptor: $1,500-$3,000
- Shadow copy recovery: $3,000-$7,000
- Complex forensic recovery: $7,000-$15,000
- Negotiation service: $5,000-$15,000 + ransom amount
Cyber insurance typically covers 100% of recovery costs. We provide documentation for claims. Call 1300 723 628 for exact quote for your situation!
Q3: We lost our BitLocker recovery key. Can you help?
A: Possibly – depends on several factors. BitLocker key recovery success depends on:
- ✅ Microsoft Account: Check account.microsoft.com/devices – key might be saved there
- ✅ Azure AD: Business machines often have keys in Azure portal (admin access required)
- ✅ Active Directory: Domain computers store keys in AD (IT admin can retrieve)
- ⚠️ Forensic Recovery: If system was recently running, we attempt key extraction from RAM/hibernation (40-70% success)
- ❌ Cold Storage: If drive been offline for months with no memory dumps, forensic recovery very difficult (10-30% success)
First step: Search THOROUGHLY for key (email archives, documentation, printouts). Second step: Call 1300 723 628 – we’ll assess if forensic recovery viable before you pay anything.
Q4: How long does business recovery take?
A: Timeline varies by recovery method:
- ⚡ Emergency assessment: 2-4 hours (phone/remote)
- 📊 Known decryptor: 1-2 days (identification + decryption)
- 💾 Shadow copy recovery: 2-5 days (extraction + verification)
- 🔬 Forensic analysis: 3-7 days (memory dumps, key extraction attempts)
- 💰 Negotiation: 5-10 days (communication with criminals is slow)
Partial Operations: For businesses, we prioritize CRITICAL files (current projects, customer orders, today’s appointments) for recovery within 24-48 hours while complete restoration continues. This allows business operations to resume faster even if full recovery takes longer.
Q5: Will our cyber insurance cover recovery costs?
A: YES – most cyber insurance policies cover ransomware recovery. Typical coverage includes:
- ✅ Professional recovery fees ($1,500-$15,000+)
- ✅ Forensic investigation costs
- ✅ Negotiation service fees
- ✅ Ransom payments (if approved by insurer)
- ✅ Business interruption losses
- ✅ PR/crisis management
- ✅ Legal consultation
Important: Most policies require 24-48 hour notification of incident. Contact your cyber insurance provider IMMEDIATELY after ransomware discovery. We provide comprehensive documentation for claims: incident reports, forensic analysis, itemized invoicing, recovery verification. Our documentation ensures claims get paid (95% reimbursement success rate).
Q6: Can you recover encrypted files without the key/password?
A: Depends on encryption type and circumstances:
- ✅ Weak/Old Encryption: Possible via brute force or known vulnerabilities
- ⚠️ BitLocker/FileVault (Recent Use): 40-70% via forensic key extraction from RAM
- ⚠️ Ransomware (Known Variants): 25% have free decryptors available
- ⚠️ Partial Encryption: 30-60% of files recoverable if encryption incomplete
- ❌ Modern Encryption (AES-256): Cannot brute force in reasonable timeframe
- ❌ Modern Ransomware: Military-grade encryption, no decryption without key
Honest answer: Modern encryption is DESIGNED to be unbreakable. If you have AES-256 BitLocker from 2 years ago and no key anywhere, recovery probability is very low (10-20%). We’ll assess your specific situation and give honest probability BEFORE charging. Don’t waste money on impossible recovery!
Q7: What’s the success rate for ransomware recovery?
A: Highly variable based on scenario:
- 95-100%: Known ransomware with free decryptor
- 70-90%: Shadow copies intact, offline backups exist
- 60-75%: Negotiation + payment (40% of payers never get working decryptor)
- 40-70%: Forensic key recovery from RAM/hibernation
- 30-60%: Partial encryption, interrupted ransomware
- 10-30%: Modern ransomware, no backups, no decryptor, negotiation failed
Key Factor: BACKUPS. Businesses with offline backups have 90%+ recovery success. Businesses with NO backups and modern ransomware have 30-40% success (heavily dependent on negotiation outcome). This is why backup strategy is critical BEFORE attack occurs!
Q8: We’re a law firm with client privilege concerns. How do you handle confidentiality?
A: We understand legal obligations and provide appropriate protections:
- 📝 NDA Standard: We sign comprehensive Non-Disclosure Agreements
- ⚖️ Privilege Protection: We understand attorney-client privilege, won’t review file contents
- 🏢 On-Site Service: For highly sensitive cases, we work at your office (data never leaves premises)
- 🔐 Secure Transport: If systems must leave office, encrypted secure containers used
- 👥 Limited Access: Only senior analysts (with security clearances) work on legal/medical/financial cases
- 🗑️ Certified Destruction: All forensic copies securely wiped and certified destroyed post-recovery
- 📊 Chain of Custody: Full documentation if recovered data needed for evidence/litigation
We’ve worked with dozens of Australian law firms, medical practices, and financial services companies. Your confidentiality is our highest priority. Call 1300 723 628 to discuss security protocols!
🚨 Business Data Emergency? We Provide Same-Day Response!
Your business operations are halted. Clients are calling. Deadlines are approaching. Every hour costs thousands in lost productivity and mounting liability. Ransomware and encryption emergencies represent existential threats to businesses – we understand that recovered data = business survival.
Don’t let encryption destroy your business. Most scenarios ARE recoverable with expert intervention!
📞 CALL NOW FOR EMERGENCY BUSINESS RECOVERY:
✅ 24/7 emergency response – ransomware doesn’t wait for business hours
✅ Same-day Melbourne service – technician at your office within 4 hours
✅ Forensic expertise – $50,000+ in specialized recovery tools
✅ Business-first approach – critical files recovered first
✅ Cyber insurance partnership – comprehensive claim documentation
✅ No Data, No Fee – you only pay if we successfully recover your data
✅ Honest success rates – realistic expectations, no false promises
📍 Business Service Areas:
Melbourne (same-day on-site service) | Sydney (next-day express) | Brisbane | Perth | Adelaide | All Major Australian Cities
🔗 Related Business Services:
- Complete Data Recovery Services – All business data loss scenarios
- SSD Data Recovery – Business laptops, servers with SSD failures
- NAS Data Recovery – Business file servers, network storage
- External Drive Recovery – Business backup drives
⚠️ CRITICAL FOR BUSINESS OWNERS: Do NOT pay ransomware demands without professional assessment! Do NOT attempt DIY decryption! Do NOT delay – encryption emergencies worsen with time. Call 1300 723 628 immediately for expert guidance. Every hour you wait reduces recovery probability and increases business impact. We provide same-day emergency assessment – call now!
💼 Our Promise to Australian Businesses: We understand that your business data represents customer trust, professional obligations, and years of hard work. Ransomware and encryption emergencies are business-critical events requiring immediate expert intervention. We provide the specialized forensic expertise, business-first approach, and confidential handling that Australian businesses deserve. Trust The Original PC Doctor with your business continuity. Call 1300 723 628 now – 24/7 emergency response available!